Next-level security for your peace of mind
You worked hard for your money. Here's how River keeps it safe.
How River protects your funds
Proof of Reserves
Multisig cold storage
Custody not built on third-parties
FDIC-insured cash at Lead Bank
How River protects your account
2-factor authentication
Account notifications
24/7 security monitoring
SOC II compliance
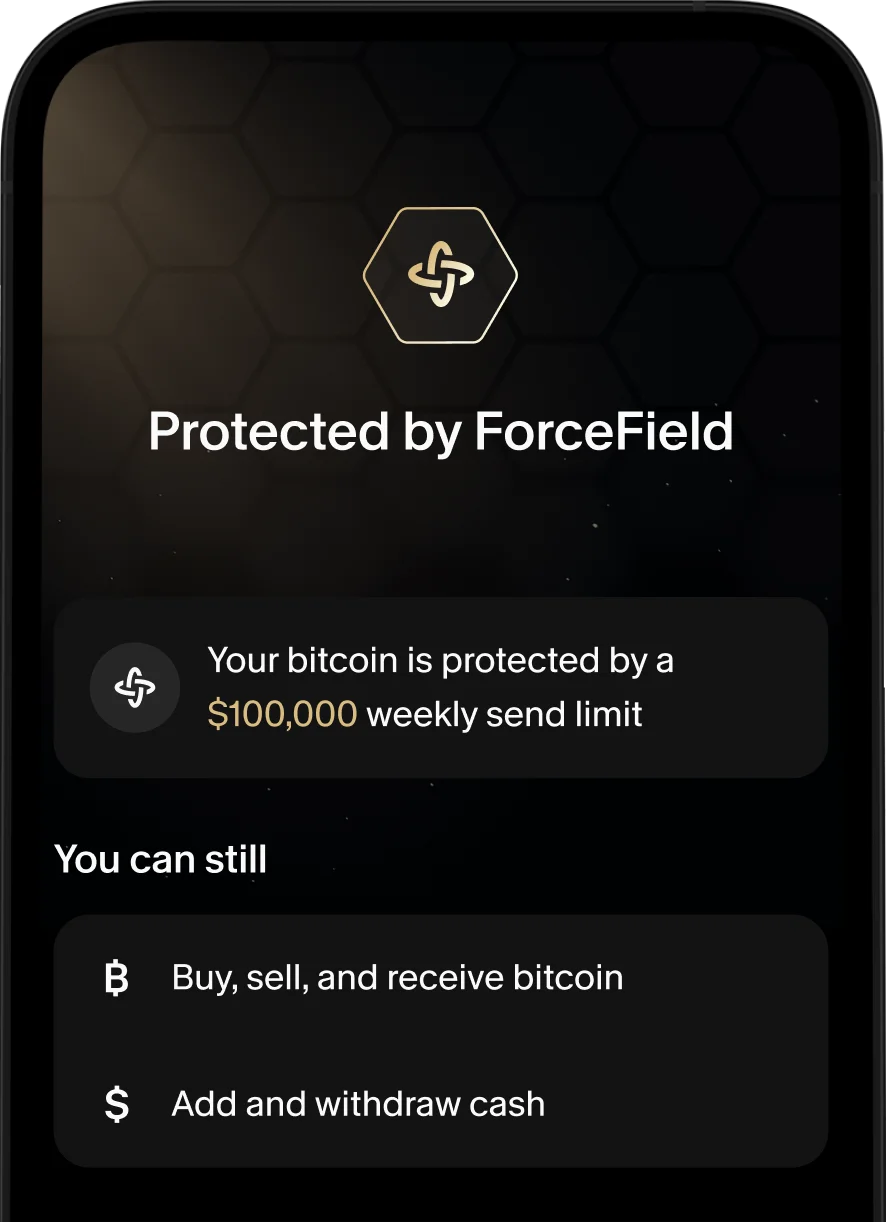
Send limits with ForceField
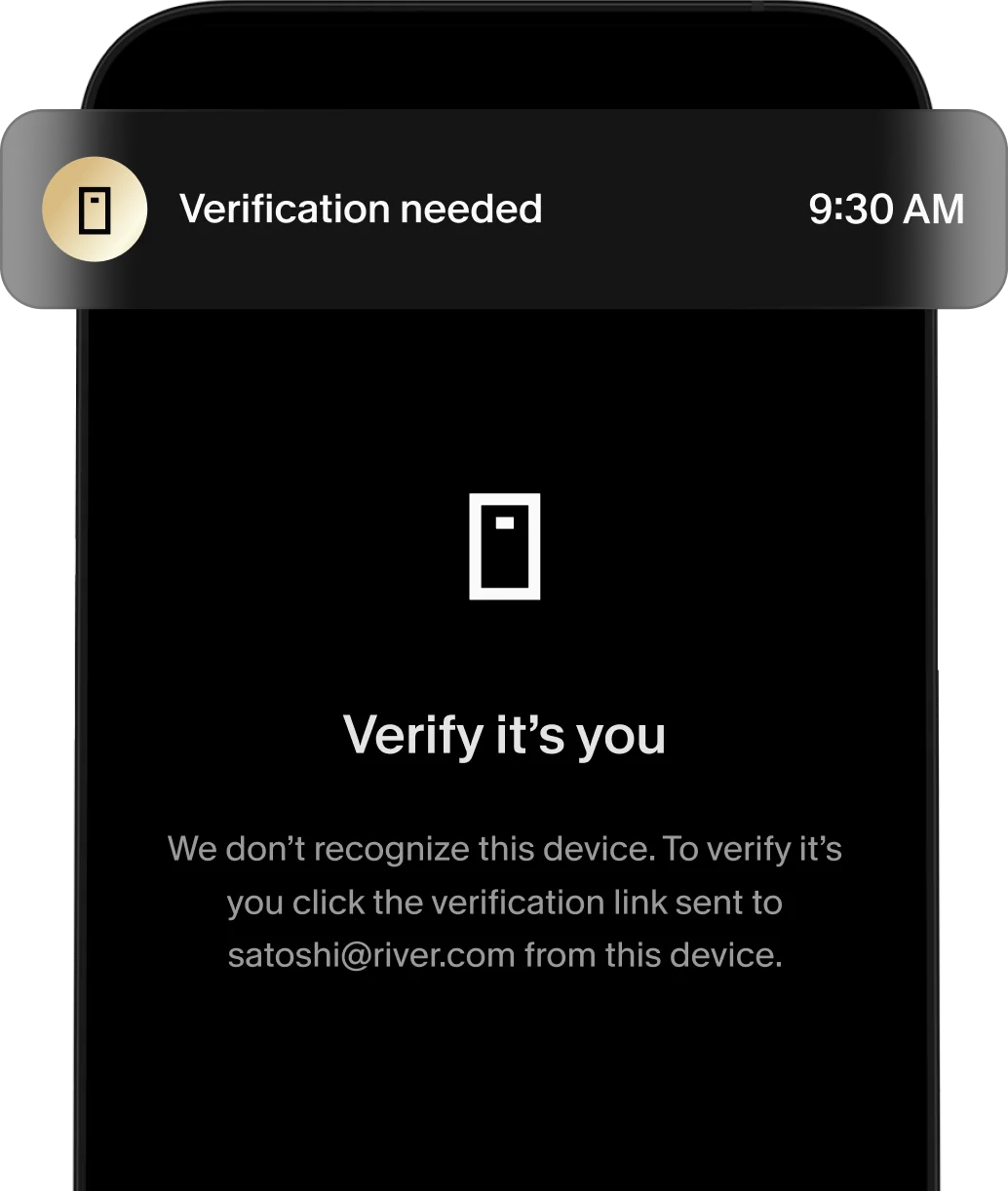
New device verification
Proof of Reserves
Verify your bitcoin holdings
River publishes monthly Proof of Reserves so you can verify that we hold the bitcoin we say we do. We do not lend out your bitcoin.

River has the highest security standards
FDIC insured cash up to $250,000¹
Your cash is FDIC insured up to $250,000¹.
Multisig cold storage
100% of client bitcoin deposits are kept in cold storage after being purchased, meaning they are isolated from the Internet.
SOC II compliance
River has strict data controls across its systems and is SOC II compliant.
Custody not built on third parties
River has full control over its bitcoin custody infrastructure to minimize dependencies on third parties.
Account security you can't get elsewhere
A ForceField for your bitcoin
Add another layer of security to protect your bitcoin in the event of device theft or loss, stolen login credentials, scams, and phishing attacks.
Intelligent account security
We offer security features to help clients protect their funds and personal information. This includes 2-factor authentication, device verification and 24/7 monitoring.
Ask your Bitcoin exchange the hard security questions
Vulnerability Disclosure Program
We encourage security researchers to partner with us in enhancing River's security. To report a security vulnerability or explore details about our disclosure program, please refer to our security.txt file by clicking the button below.

Do you have more security questions or concerns?
Disclosures