In the context of Bitcoin, a private key is what proves ownership of the funds corresponding to a given address. The private key is used to create signatures which are required to spend bitcoin.
Private key and public key
Bitcoin uses public key cryptography to create a key pair—a corresponding public and private key—that controls ownership of bitcoin. The public key is used to receive bitcoin, while the private key allows a user to sign transactions by creating a digital signature and thus spend the bitcoin. When a user presents a public key and signature, anyone on the Bitcoin network can verify and accept a transaction as valid, confirming that the user spending the bitcoin is the true owner of the funds.
How is a private key generated?
Private keys are usually generated by a user’s Bitcoin wallet. However, the user almost never has to see or directly interact with their private keys as their wallet handles all of the complex math behind the scenes.
Bitcoin wallets use an industry standard to derive private keys. First, the wallet uses a secure random number generator to generate a seed, which can then be used to derive as many keys as are needed by the user. This setup allows the wallet to backup only one seed and not each unique private key.
How private keys are used in a transaction
We will use a sample transaction to better illustrate the process of how private keys are used in the Bitcoin network.
If Bob wants to send Alice one bitcoin, the transaction would take place as follows.
- Bob opens his wallet and enters Alice’s public key into the recipient field of the wallet.
- The wallet software creates a transaction and signs it using Bob’s private keys. If the digital signature that is generated corresponds to the funds Bob is attempting to send, the transaction will be accepted as valid by the Bitcoin network.
- The funds now can be accessed by whoever owns the private keys that correspond to Alice’s public key. In this case, that is Alice, as she is the only one who holds that private key.
Private keys and digital signatures
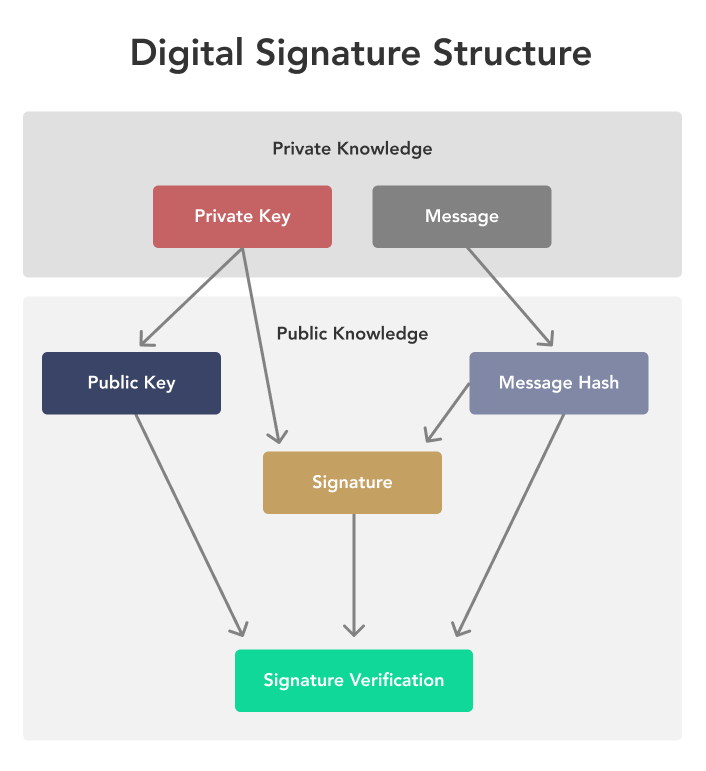
As in the example above, private keys are used to create signatures. A signature is a piece of data that can only be created or calculated using the private key. However, the validity of a signature can be verified using only the public key. This allows a private key to serve as an unforgeable identity. In the context of Bitcoin, this feature is used to ensure that bitcoin can only be spent by its rightful owner, who controls the corresponding private keys.
How do I store my bitcoin private key?
When you own Bitcoin, what you really own is a private key to control those funds on the blockchain. If you lose your private keys and do not have the seed phrase of the wallet, you lose access to any funds associated with those private keys. Thus, it is important to store your private keys in a secure setup and with backups. There are several good rules of thumb when choosing a wallet to secure your keys.
➤ Learn more about choosing a Bitcoin wallet.
Cold storage vs. hot wallet
When storing large amounts of bitcoin, a cold storage wallet is considered best. For most users, this takes the form of a hardware wallet—a small device that stores a user’s private keys. Popular hardware wallets include Ledger Nano S and a Trezor One. For convenient and fast access to their bitcoin, many users prefer hot wallets—an internet-connected software application that stores a user’s private keys. This typically takes the form of a web or mobile app.
Both cold storage and hot wallets solutions have trade-offs. With cold-storage, the user is responsible for the security of their keys, without recourse to a third party in the event that they lose their device or seed phrase. This is known as self-custody. As a result, what is most secure for one user, cold storage for example, may not be the most secure solution for another.
➤ Learn more about Bitcoin cold storage.
Key Takeaways
- A private key is used to unlock and send bitcoin. It corresponds to a single public key which receives bitcoin, which are then spendable with the private key.
- Ownership of bitcoin is directly based on control of private keys. Anyone who knows a private key controls all bitcoin under that key.
- Private keys are nothing more than very large numbers. However, guessing a valid private key is far more difficult than guessing a credit card and pin number.


