Cryptography is a field of math which encompasses a variety of different methods for maintaining digital security and privacy. Encryption and decryption, hash functions, and digital signature algorithms are all areas of study within the field of cryptography. Bitcoin is known as a cryptocurrency because it makes use of cryptography to implement a decentralized monetary system and enable fully digital peer-to-peer payments.
Bitcoin is far from the only technology to use cryptography. Today, all but the simplest electronic devices use some form of cryptography to protect sensitive information and verify digital identity. Password-protected phones and computers, governments, telecommunication networks, banks, social media, and more all implement cryptography for reliable security.
Encryption and decryption
Encryption is the process of converting data into secret, incomprehensible code such that only intended parties are capable of understanding the information. The process of encryption transforms the original data, known as plaintext, into a secret code known as ciphertext. The opposite process, known as decryption, transforms the ciphertext back into plaintext.
Encryption is used by almost every digital device and service in order to protect data against unauthorized parties or malicious attackers. Strong encryption allows users to safely browse the internet, securely protect their data with passwords, and message one another in privacy.
There are many types of encryption schemes, each with different levels of security. In most cases, one or more keys are used to encrypt and decrypt the data. The type and number of keys required depends on the encryption scheme. Some encryption schemes are thought to be secure against even quantum computers, while others have been proven insecure against regular computers or human calculations.
Encryption and Bitcoin
The Bitcoin network and database itself does not use any encryption. As an open, distributed database, the blockchain has no need to encrypt data. All data passed between Bitcoin nodes is unencrypted in order to allow total strangers to interact over the Bitcoin network.
However, some Bitcoin services require more security and privacy. In order to securely store private keys, most Bitcoin wallets encrypt their data using a variety of encryption schemes. For example, Bitcoin Core encrypts its wallet using the Advanced Encryption Standard (AES). This is the same encryption algorithm used by the NSA for its classified information, and AES is considered extremely secure. In order to decrypt a Bitcoin Core wallet, a user must enter their password, which is used as the decryption key.
Hash functions
A cryptographic hash function is a mathematical function which takes any data as input and produces an output with special characteristics. There exist many instances of hash functions, but all hash functions share these core characteristics, which make hash functions extremely useful not only for Bitcoin, but for many digital systems. The output of a hash function is called a hash or a digest, and it is a large number usually represented as a string of letters and numbers in hexadecimal notation.
While the input to a hash function can vary infinitely, the output of a cryptographic hash function is always of a certain length. The length of the output depends on the specific hash function used. For example, SHA-256, a member of the Secure Hashing Algorithm family of hash functions, will invariably output 256 bits of data no matter how large or small the input is.
The output of a cryptographic hash function is also deterministic, meaning that the same input given to the same hash function will always yield the same output. However, if a single character or byte of data is changed in the input, the new output will not resemble the old output in any way.
This property is critical to a hash function’s utility as it enables rapid verification of arbitrarily large data. For example, if Alice has a large file, and she wants to verify that it has not been tampered with, she can compare the hash of the file from when she last verified it to the current hash of the file. If the file is unchanged, the two hashes will match exactly. However, even the smallest change will result in almost all of the characters of the hash being changed.
Lastly, the output of a cryptographic hash function is a random, one-way function. This means that the input cannot be predictably formed to yield a desired output. Additionally, an output does not display any information about the input, and thus, an output cannot be used to derive an input.
This property is useful for several reasons. Because it is a one-way function, a hash can be used as a commitment to certain information without revealing the information being committed to. The randomness of hash functions also makes them useful for Bitcoin’s Proof-of-Work system.
Hashing and Bitcoin
The Bitcoin protocol mainly uses SHA-256 for all hashing operations. Most importantly, hashing is used to implement Bitcoin’s Proof-of-Work mechanism. A hash is a large number, and in order for a miner to submit a block to the network, the hash of the block must be below a certain threshold. Because hashing is a random, unpredictable process, finding a valid hash can only be achieved through intensive guessing.
➤ Learn more about Bitcoin mining.
The properties of hash functions also ensure Bitcoin’s immutability. Inside each block, a Merkle tree is constructed by calculating a single hash of all transactions in a block. This ensures that every transaction is immutable once included in a block.
Each block also guarantees the immutability of preceding blocks. This is accomplished by including the hash of the previous block in every block, meaning that once a block is added to the blockchain, it cannot be altered.
➤ Learn more about Merkle trees.
Digital signatures
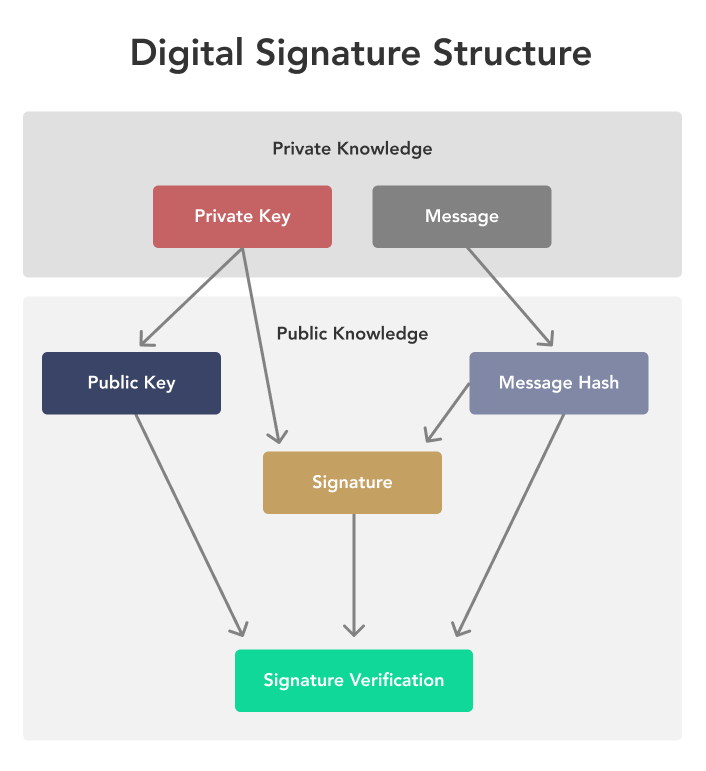
A digital signature is similar to a physical signature, yet far more secure and trustworthy. Like its physical counterpart, a digital signature connects approval of the data being signed to the specific identity of the signer. Unlike a physical signature, a digital signature cannot be copy-pasted because a signature is unique for each piece of data being signed.
There are three parts to a digital signature: the data being signed, the public key of the signer, and the signature itself. The data can be anything digital, including text, an image, an audio file, and more. The public key is a pseudonymous form of identity, informing the public that the owner of the corresponding private key has signed this message. Lastly the signature is mathematical proof that the owner of the public key and the corresponding private key signed the exact data provided.
The magic here is that the private key is required to create the signature, but not required to verify it. Anyone can verify that the signature is valid using only the public key, the signature, and the message. Furthermore, since the signature is generated using the hash of the data it is signing, verifiers can be sure that the data provided is unaltered since it was signed.
Digital signatures and Bitcoin
Bitcoin implements a digital signature algorithm called ECDSA which is based on elliptic curve cryptography. While ECDSA allows a private key to sign any type of message, digital signatures are most frequently used to sign transactions and send bitcoin.
The Bitcoin protocol allows pieces of bitcoin called UTXOs to be sent to a public key, such that only a valid signature from the corresponding private key can unlock it. This signature is published to the blockchain so that any member of the Bitcoin network can verify that the signature, the public key, and the message match.
Thanks to this design, Bitcoin is a purely peer-to-peer system. A Bitcoin transaction can be sent from payer to payee without any third party taking custody of the funds. Although miners process each transaction, they are unable to produce valid signatures for other people’s bitcoin and thus unable to steal any bitcoin.
Key Takeaways
- Cryptography is a field of math and includes the study of encryption, hash functions, and digital signatures.
- The Bitcoin network uses hash functions to ensure the blockchain’s security and immutability.
- Bitcoin uses public key-based digital signatures to allow users to send bitcoin trustlessly.